So the title is a bit misleading, there is no lighter side to cryptographic hash functions. They are complex. Very. And you need a serious mathematical background to understand the different algorithms used to secure data.
Since the development of rotor cipher machines in World War I and the advent of computers in World War II, the methods used to carry out cryptology have become increasingly complex and its application more widespread.
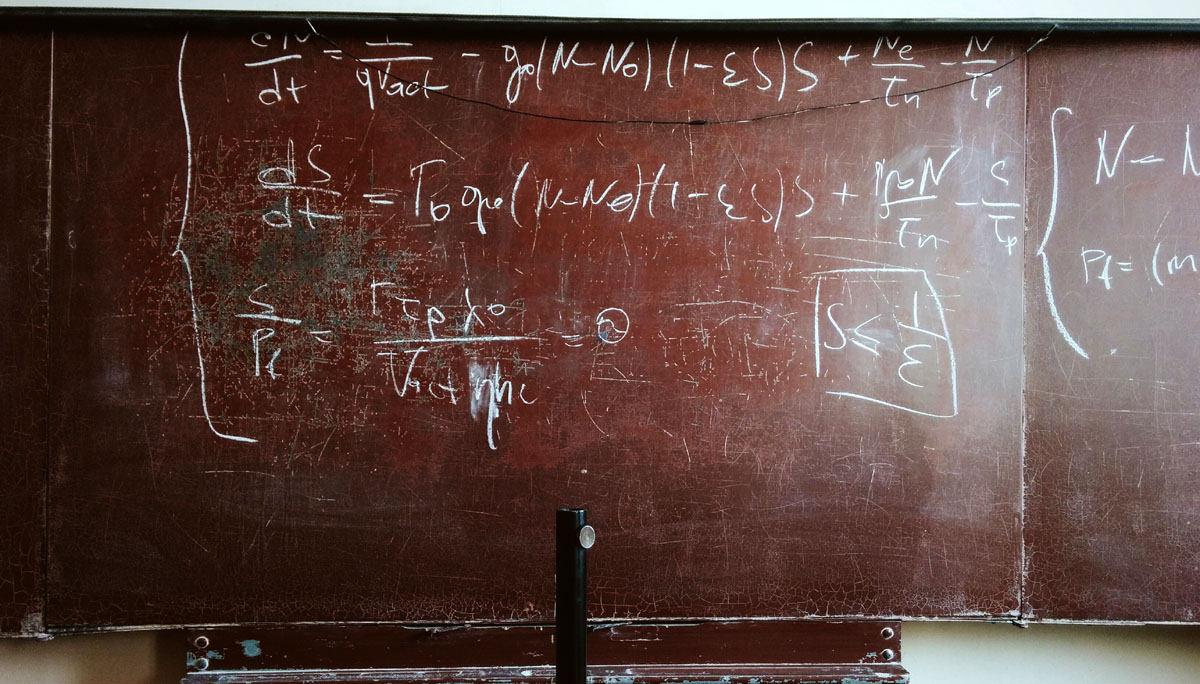
Modern cryptography is heavily based on mathematical theory and computer science practice; cryptographic algorithms are designed around computational hardness assumptions, making such algorithms hard to break in practice by any adversary. It is theoretically possible to break such a system, but it is infeasible to do so by any known practical means. These schemes are therefore termed computationally secure.
Why are cryptographic hash functions important to cryptocurrencies? In essence, they are used for managing the addresses of information in the blockchain (each block has an address) and they are also used for securing (or hiding) the information from potential attackers.
For more information on the cryptographic hash function used for Bitcoin, I have put together a page with a SHA256 (the cryptographic hash function used by Bitcoin) calculator. This is a simple practical example of how raw data is encoded into a fixed length string. The page can be found here.